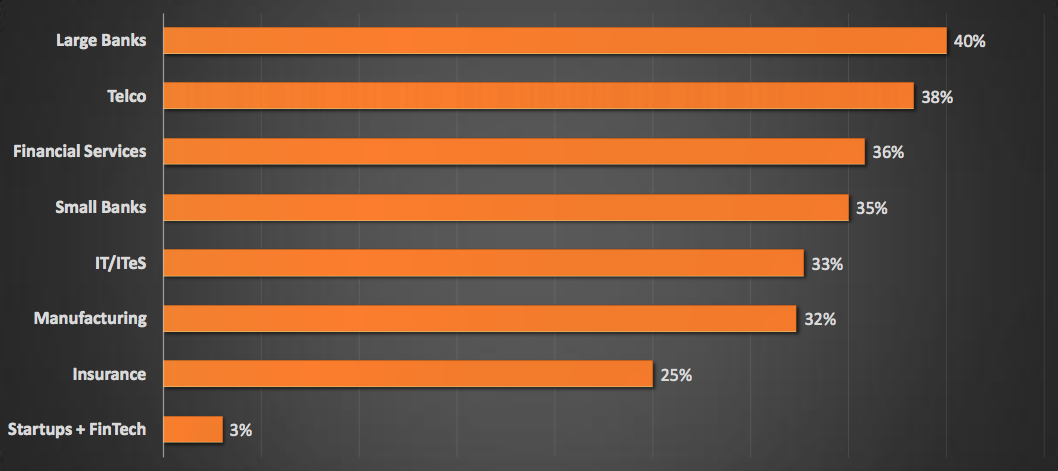
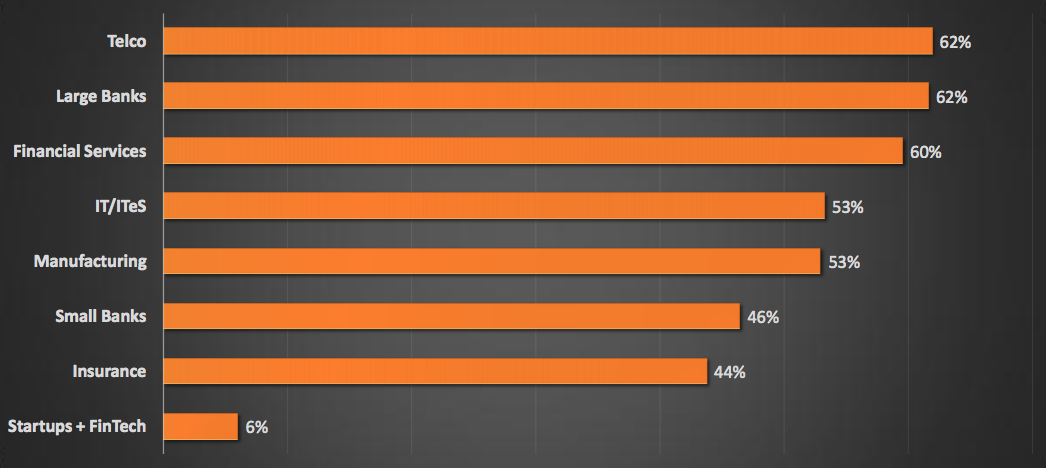
Security Maturity Score By Industry :
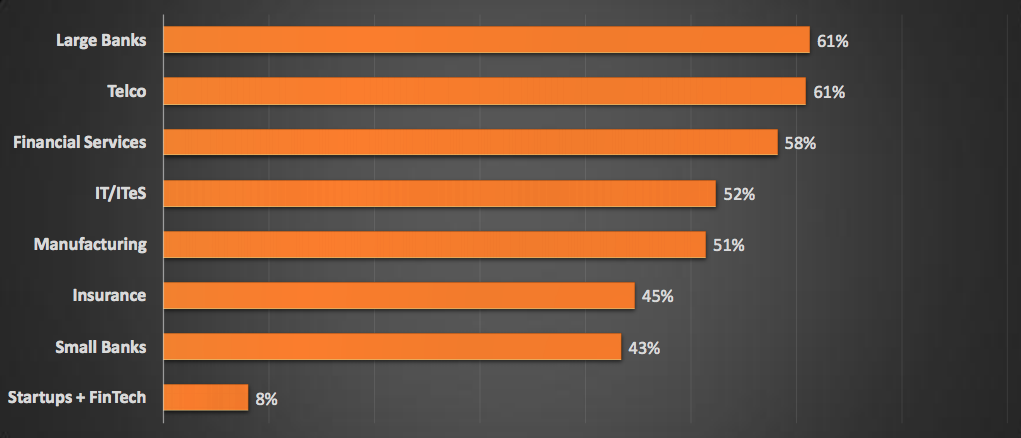
Identification Capabilities By Industry :
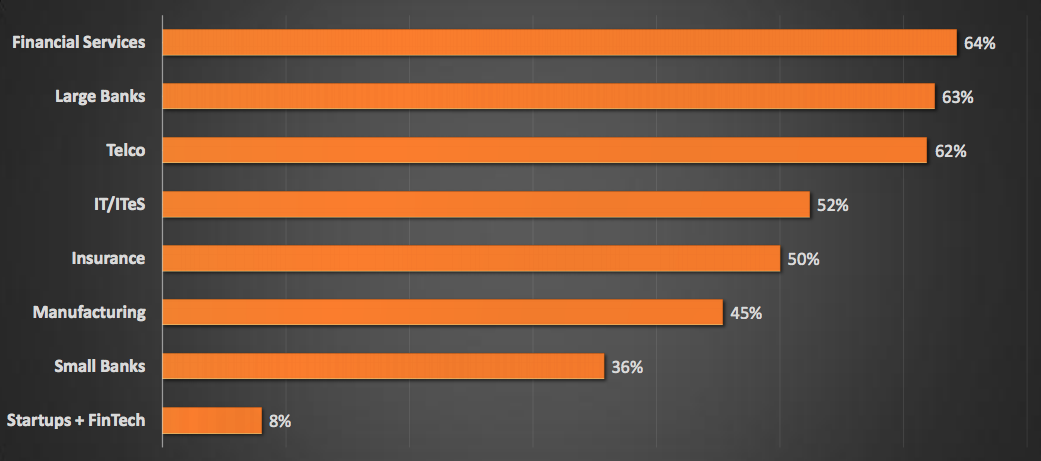
Prevention Capabilities By Industry :
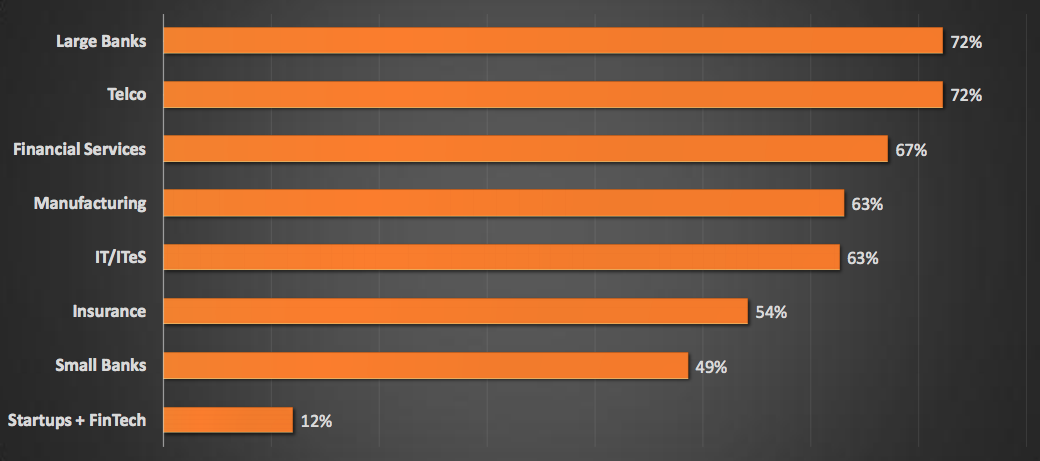
Detection Capabilities By Industry :
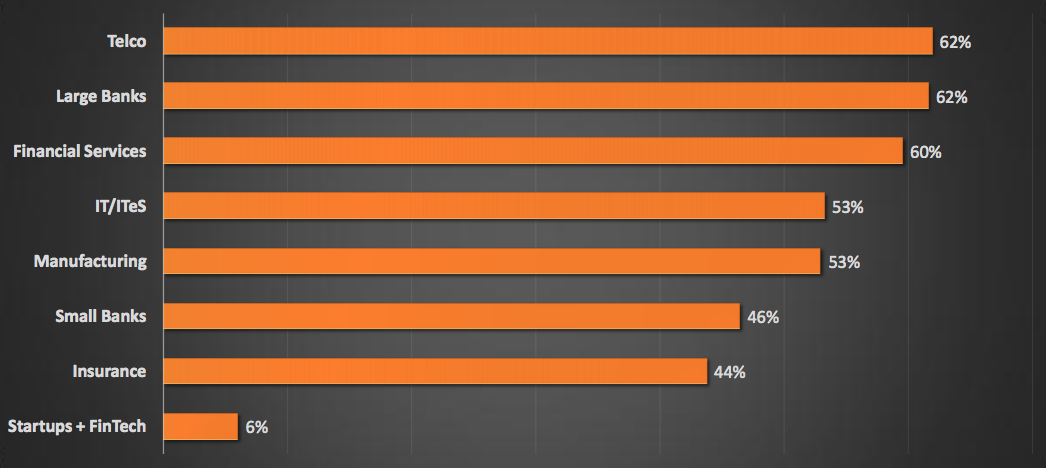
Response Capabilities By Industry :
Key Findings :
- Large Indian
Security Maturity Score By Industry :
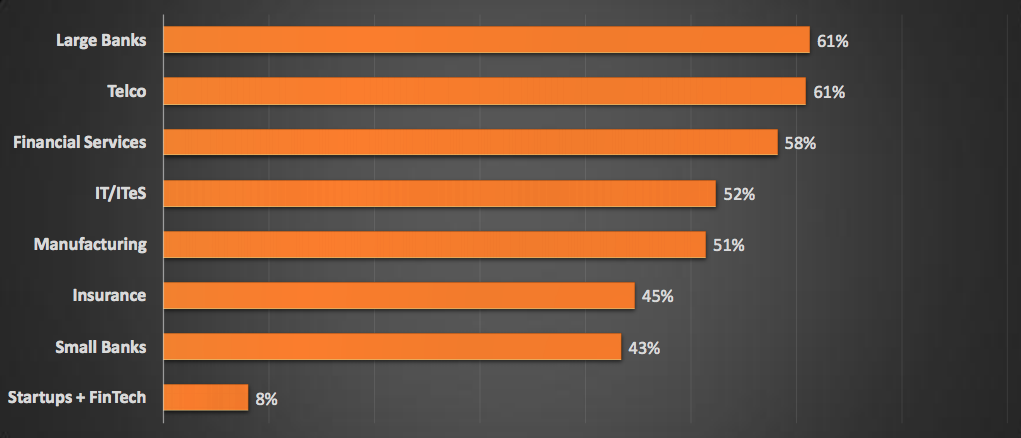
Identification Capabilities By Industry :
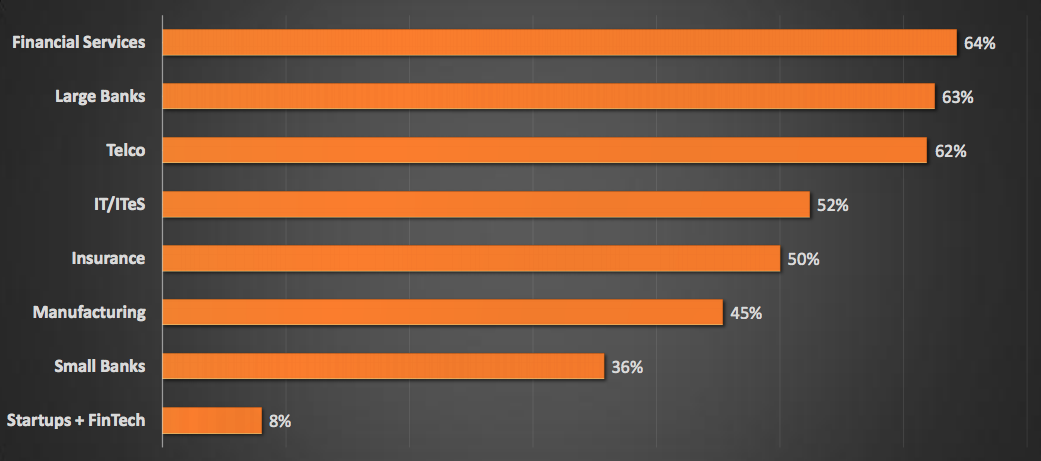
Prevention Capabilities By Industry :
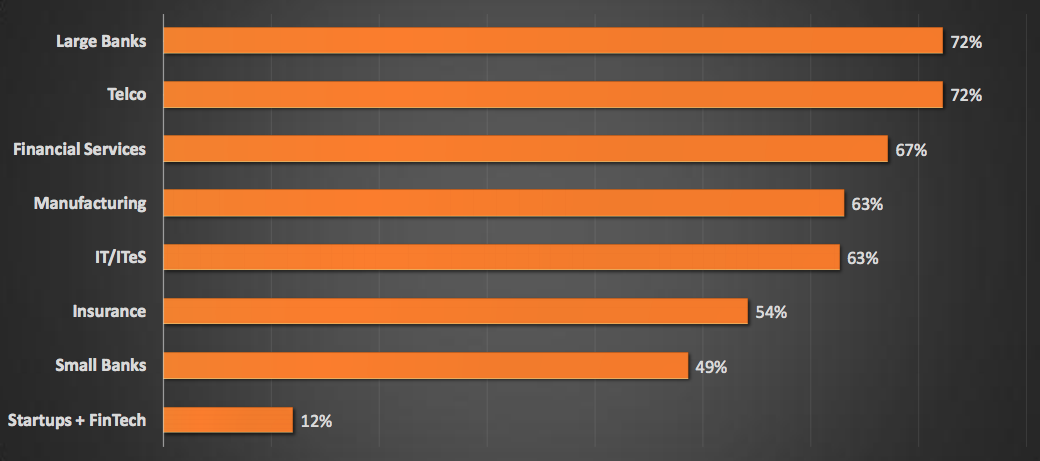
Detection Capabilities By Industry :
Response Capabilities By Industry :
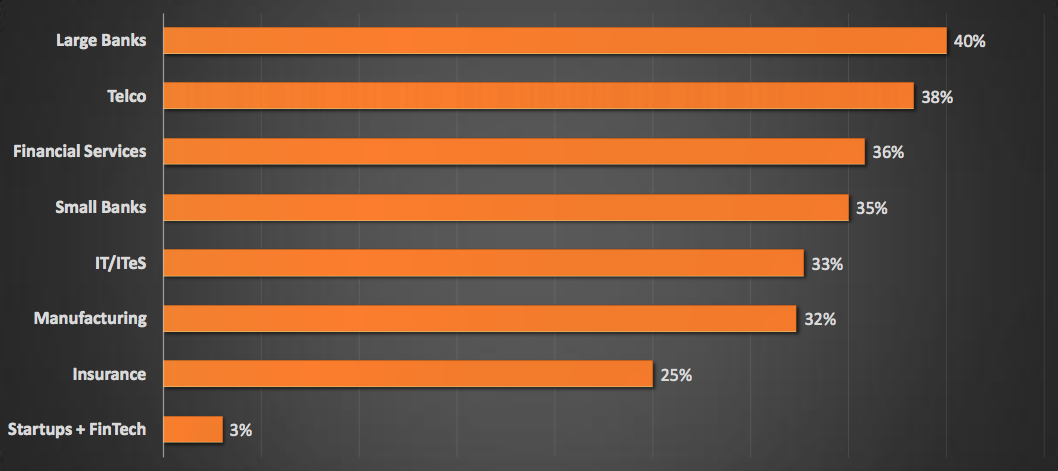
Key Findings :

We are happy to share that FireCompass has been selected as a winner of NASSCOM’s 2017 Emerge 50 award. At FireCompass our vision is to transform the way enterprises make security strategy and buying decisions.
Here is the list of top 5 vendors emerging Threat Hunting tools, but before that let us understand what threat hunting exactly refers to.

We are super excited to have Terry Cutler (voted #1 Top Influencer in CyberSecurity by IFSEC Global 2018) do a web conference as part of our Kids Cyber Safety Initiative. As a part of his talk he will talk about internet safety for students, social
Here we will explore the Shadow IT Risks for OT Departments. Operations Technology groups can be an integral part of important business functions like production, maintenance and more. This means there are a lot of IT related functions which can be
If you’re thinking that the industry you’re operating in is safe from cybersecurity threats then you might have to think again. In this article, we’ll specifically discuss the implications of breaches on healthcare businesses and why is annual penetr
As our world embraces a digital transformation, innovative technologies bring greater opportunities, cost efficiencies, abilities to scale globally, and entirely new service capabilities to enrich the lives of people globally. But there is a catch.
Topic of discussion : The Talent Shortage in Cybersecurity
Listen To Podcast: https://player.captivate.fm/episode/6c842a64-cff1-4119-beb3-1989940c47cf
Thank you Katelyn Ilkani, I thoroughly enjoyed discussing the challenges of the talent shortage in cy
(this is cross-posted from Anton on Security)
As I am expanding my responsibilities to cover some exciting data security topics (like, say, our cloud data discovery DLP), I wanted to briefly discuss a few broader issues I have noticed related to moder
This post is my admittedly imperfect attempt to “reconnect” data security controls to threats. It is also my intent to continue pulling on the thread I touched in this post— so expect more posts about that.
Let’s first get this out of the way: there a
CISOPlatform is hosting Breakfast meetup @ San Francisco. Join us if you are interested.
Register Here : https://www.cisoplatform.com/profiles/blogs/meet-ciso-platform-at-rsa-conference-2024
CISOPlatform Summit: Stronger Together As A Community.
Join us on 30th May, Thursday, Shangri-La at Bangalore
Register Here : https://events.cisoplatform.com/cisoplatform-summit-2024
(Train Your Team) Trainings From Past Blackhat/Defcon/Nullcon Trainers
Register Here : https://event.cisoplatform.com/sacon/