Setting the Scene: The Rising Stakes in Cybersecurity
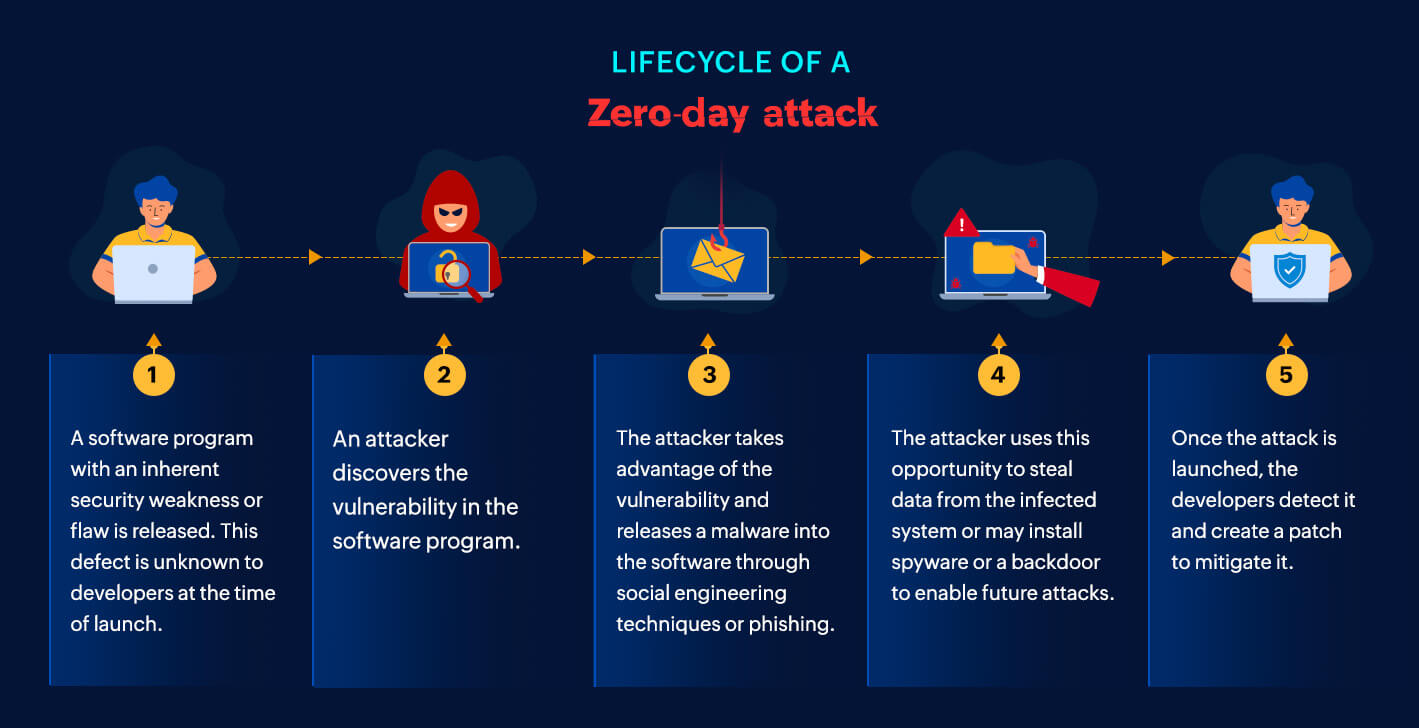
The cyber threat landscape isn’t just expanding—it’s convulsing. Ransomware, state-sponsored hacks, and zero-day exploits are wreaking havoc faster than organizations can respond. Yet, the workforc